Over the years, we’ve gained a reputation for providing support that is above average for the hosting industry. Obviously it helps that the average is really quite low, and simply providing helpful answers in a timely manner puts you some way above it, but we’re proud of this reputation and work hard to provide the best support that we possibly can.
So what do we do differently?
Perhaps the biggest thing is that we don’t have any dedicated support staff.
Our support rota
Our support queue is staffed by a rolling rota that includes all of our technical staff. The staff responsible for managing our routers, running our DNS servers, developing our control panel and maintaining all our other infrastructure, all take it in turns to do regular days on “first line support”. And, yes, this includes our founders & directors.
The most obvious benefit of this is that customers get straight through to someone who can actually deal with their issue — all tickets are effectively escalated to what might elsewhere be considered second, or more likely third, line support, but without the hassle of fighting your way past chat bots and scripted replies.
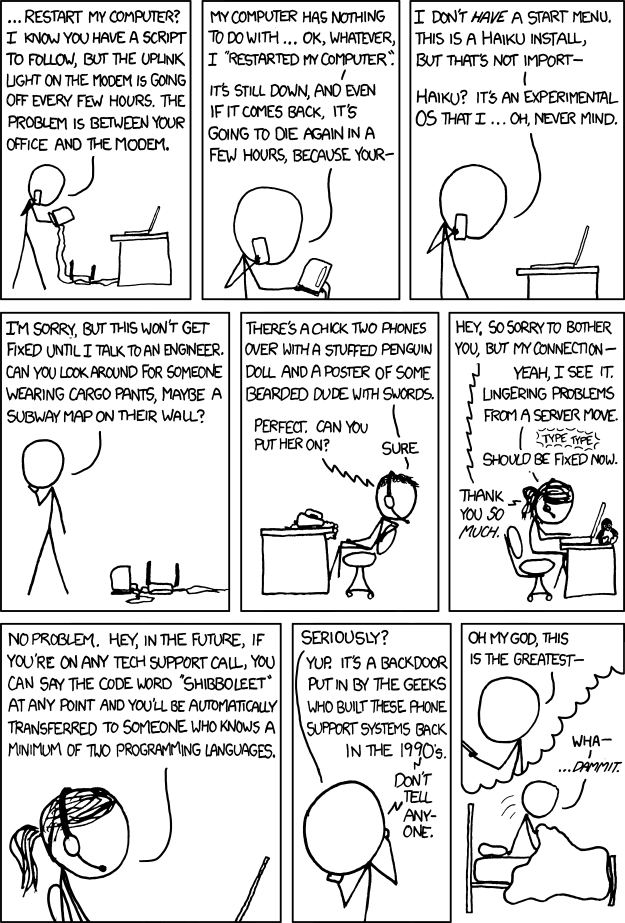
There’s no need to say “Shibboleet” to our staff.
That’s obviously better for the customer, but conventional wisdom is that good technical staff are too expensive to put on first line support, and you won’t retain them if you do.
Our company trades on its reputation for good support, so cost cutting here would be a false economy, and you only have to look at the likes of Stack Overflow and Quora to see that many technical experts enjoy using their knowledge to help others.
It is true that our staff probably wouldn’t want to do support full-time, but mixing support with normal responsibilities actually provides some useful variety, and has a number of other benefits.
Direct customer feedback
One of the most valuable benefits of this arrangement is the direct contact between our technical staff and our customers. Our staff get to see directly what our customers want to do, and what parts of our website and systems our customers find confusing. They’ve also got a strong incentive to improve them so that they don’t find themselves answering the same simple questions again and again when on support, and because our “support staff” are also the people responsible for those systems, they’re in a position to actually fix them.
Perhaps one of the best measures of how well this works is that the average time to deal with a support ticket has gone up over the years. All the easy support tickets that we used to be able to clean up before the first coffee in the morning have gone, because the customer did it themselves the night before. The tickets in the support queue are getting harder, and this is good thing (and yet another lesson in the hazards of optimising for KPIs).
Why we prefer email support
Our rolling rota of support staff is one of the reasons why we insist on email for support. Having a written record of all communications on a ticket makes it much easier to hand tickets from one person to the next. Customers don’t have to spend time explaining an issue each time it’s passed to a different member of staff – although for more complicated tickets, we do quite often ask the person who first picked it up to carry on with it, even if they’re no longer on support.
How far will this approach scale?
We’ve operated this system for quite a few years and the amount of time we spend dealing with support queries has grown steadily with the company.
We’ve no plans to change this approach, but it’s quite possible that there will come a point where it makes sense to hire staff whose primary role is support. Like all things, the more you do, the better you get, and one of the costs of our approach is that using non-dedicated staff is inefficient — they’re more likely to have to look things up or check with colleagues when responding to tickets.
We have already taken the step of splitting out finance-related support tickets into a separate queue, which is dealt with by our finance staff.
If we do ever take that step of employing dedicated support staff we won’t compromise on the quality of support that we provide, and it’s likely to be in addition to, rather than instead of, our rolling rota, because of the benefits it provides to both us and our customers.